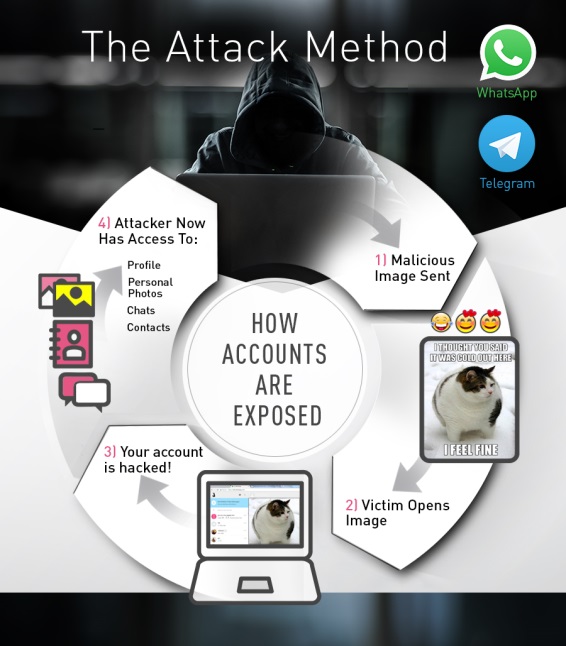
No matter how strong encryption is, as long as human interaction is there we will see encryption being exploited. WhatsApp and Telegram were exploited by a single image which resulted in a complete account take over.
How Hackers hacked WhatsApp and Telegram
As simple as it may sound, Hackers would send a special crafted link which will appear as a Image file and once the image was opened, complete access would be available with the hacker of victim account.The hack was only executable on Web versions of the chat applications.
Demo Video of WhatsApp Hack
Technical breakdown of WhatsApp / Telegram Hack
WhatsApp upload file mechanism supports a few document types such as Office Documents, PDF, Audio files, Video and images. However, Check Point research team managed to bypass the mechanism’s restriction and uploaded a malicious HTML document with a legitimate preview of an image. Such an action fools the victim into to believing that it is a authentic file type.
Once the document is opened, WhatsApp web client uses the FileReader HTML 5 API call to generate a unique BLOB URL with the file content sent by the attacker then opens the same URL.
The Attack takes place in following steps
Step 1 : First, the attacker crafts a malicious html file with a preview image. Telegram code looks like this.
Step 2 : WhatsApp web client stores the allowed document types in a client variable called W[“default”].DOC_MIMES this variable stores the allowed Mime Types used by the application.
Step 3 : Since an encrypted version of the document is sent to WhatsApp servers it is possible to add new Mime type such as “text/html” to the variable in order to bypass the client restriction and upload a malicious HTML document.
Step 4 : Client encrypts the data using encryptE2Media.
Step 5 : Change extension and preview image and you get something which has more chances of being clicked.
Step 6 : Once the victim clicks on the link on web.whatsapp.com , will see a blob and session will be hijacked. A Javascript allows attacker to check file after every X seconds for a WhatsApp session hijack.
Step 7 : Multiple sessions are not allowed by WhatsApp which is managed by this code , as it makes the victim browser stuck.giving ample time to the Attacker. While Telegram allows multiple sessions so its not required to write any code nor the victim on Telegram will be notified.









is this work now ???
not this particular trick.. but mime modification is still there ..
Hi, i’m Tyler, i had my friend help me hack my ex’s email, facebook, whatsapp,and his phone cause i suspected he was cheating. all he asked for was a his phone number. he’s email is ([email protected])..IF u need help tell him Tyler referred you to him and he’ll help. Am sure his going to help you do it, good luck
I know [email protected] is the best hacker out there when it comes to sale of tools and guide, Mobile hack, email interception, credit score repair, Grade change, DDOS, SQL Injection, Spyware program. Remove content on the internet or database.
I know of one of the best hackers who I can vouch for. He is very good and reliable. he has helped me with so many issues with my my husband’s phone, because we had issues with cheating, he was cheating a lot and he helped me hack his phone and everything without him knowing and I was monitoring everything he was doing. Just contact him for any hacking related issues like hacking phones, computers, emails. Facebook accounts, WhatsApp, Instagram. Just mail him and you will get a good hacking service. Contact him on [email protected]
hello house
i saw recommendations about this programmer ( Mr John ) online and never hesitated to contact him,He asked me for some few information about my husband mobile device,no personal info was asked for also,i provided it all to him and in less than 12 hours i was getting too see my husband text messages,Instagram ,facebook messages , viber ,iMessage ,call logs and as well as whatsapp messages as they come into her phone,i was able to get good and solid proof for my Antony to file a divorce,if you are having similar issues i would advice you contact. https://uploads.disquscdn.com/images/5c025787c03b941401a965f7f30b10233c855d656ad8402bf2b70958328f9ab5.png
As an aspiring hacker, I recognise raw talent. [email protected] is top drawer. Just assume he can do anything online but is advisable you use Tor browser for encrypting emails because there are quacks and fraudulent schemes online. justin sent you
I made use of (********@gmail.com) i saw his info on a friend’s post here i contacted him.He could help you gain access to your partner device and spy on them,you can know alot about someone through there device and email, he also does lots more relating to hacking and remote access. he his truly a genius at what he does.
he is a professional hacker that specializes in hacking related issues,you can also trust him with solving your bank issues and credit issues.You can contact him for any other hacking related problems like hacking websites, bank statement, grades and many more. he will definitely help you, he has helped a lot of people at a low cost.
.Contact him for assistance (promised to make this recommendation). wish you all the best
Wow…very interesting
great
i wanna use this to my son,,,can u teach me how to do it pliss
hey, need this application
is anyone there
is this hack still available