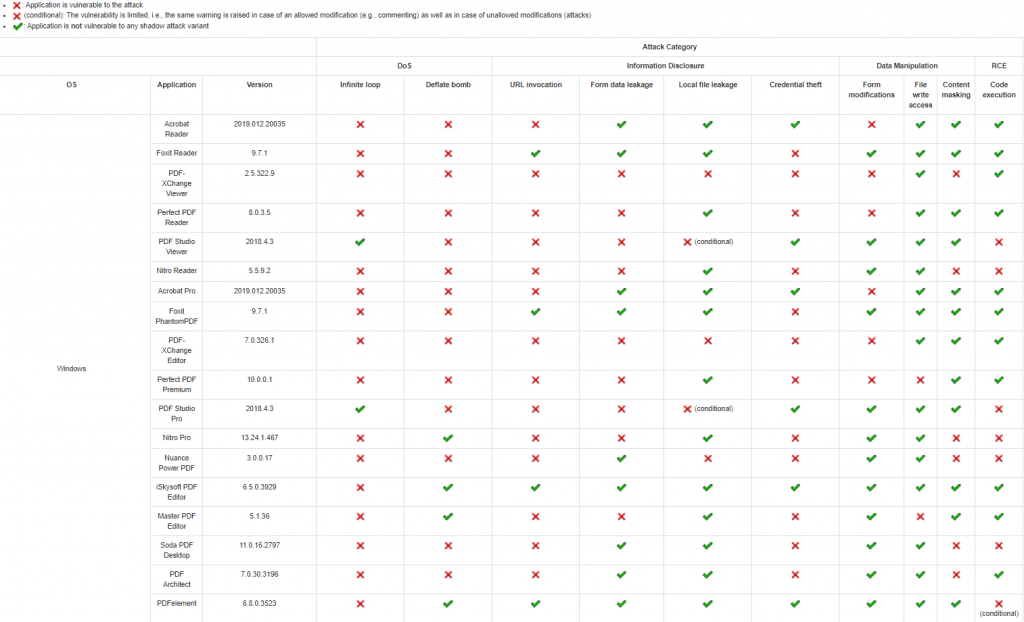
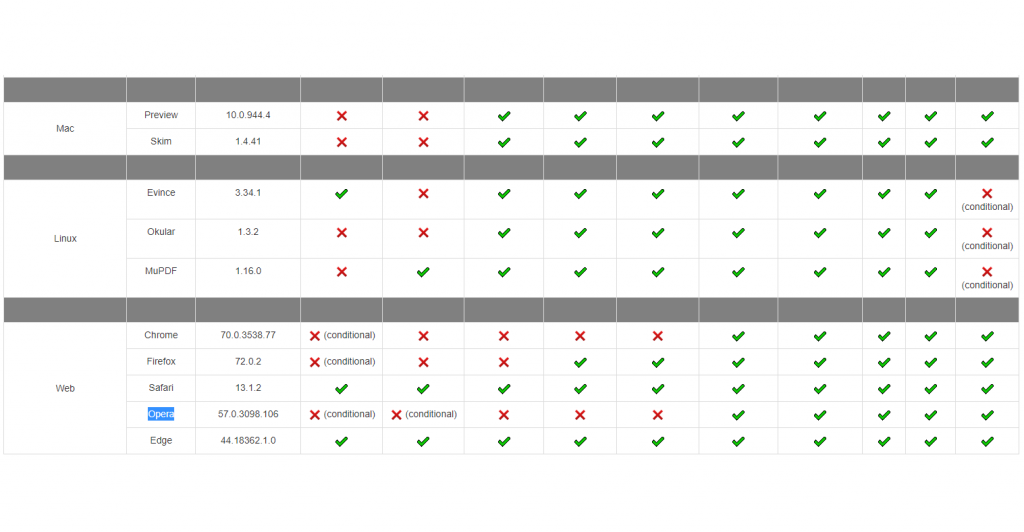
PDF Shadow attacks are essentially successful clickjacking attacks, where a hacker can hide the harmful content masked behind their bait that is digitally signed. This is the second time that the same researchers at Ruhr-University Bochum found loops to manipulate PDF Signatures. The testing was done on 28 applications running on different operating systems and the results showed that 26 of them are vulnerable to at least one Shadow Attack Variant. The evaluation of the vulnerable applications and operating systems prove that a lot of are at risk, let’s look at how and why this is possible.
Shadow Attacks affect 90% of Online Users
As of 21 Jan 2021, Google controlled 85.86% of the global search engine market share and crosses the 90% mark every now and then. This means that around 85 to 90 percent of users browsing through the internet use Chrome browser. Google Chrome is vulnerable to five of the Shadow attacks out of ten which puts 85 to 90 percent of Chrome users at risk. In other words, a whopping 80 to 90 percent of web browser users are at risk of DoS and Data breaches because of this hack. Moreover, Chrome is just one of the 26 applications that are vulnerable to the Shadow Attack. The complete list of vulnerable applications can be seen in the images below.
Why PDF Signatures are Important
PDF signature or digital signature is a type of e-signature that makes the content verified and shows trustfulness of the documents inside that PDF. Commonly e-signature uses simple authentication methods which are sued to verify the signer’s identity like their corporate ID, email address, and more. A higher level of e-signature includes an audit trail with the document.
As mentioned, above digital signatures are a type of e-signature. Certificate-based digital IDs are used to authenticate the signer’s identity show the proof of signature by binding it to the document with encryption. Moreover, the validation occurs through trusted certificate authorities (CAs) or trust service providers (TSPs).
In short, the PDF signature shows the trust level of the signer, the higher the level, the safer the document. Another neat feature here is that PDF signatures are automatically removed and the receiver of the PDF will be notified of the changes made.
However, some changes like the fonts are considered harmless, and the user isn’t alerted. These signatures are the only thing informing the receiver about the authenticity of the PDF document. All the reasons mentioned above make PDF signatures vital to ensure the authenticity of the document and its contents.
What are PDF Shadow Attacks
Shadow attacks are categorized into four classes:
- Denial of Service attack (DoS attack)
- Information Disclosure attack
- Data Manipulation
- Code Execution
- Denial of Service attack (DoS attack) makes the host’s resources unavailable for users hence disrupting the service. DoS attack is made possible by using two techniques an infinite loop or a Zip bomb. An infinite loop of functions starts taking up all your system’s memory and hanging it. A RAR file (Zip Bomb), relatively small in size is saved in the document which is automatically extracted when the viewer opens the PDF. The Zip bomb will be a few bytes in size but it will easily reach a 100+ GB size. Hence, the Zip bomb will also use most of the memory of your system and slow it down to the level that it will be unusable. Both the above-mentioned processes run in the background without the user’s consent.
- Information disclosure attack is achieved using various techniques in the Shadow Attack. The victim can be asked to input details themselves or steal data using silent background running apps. The data one is putting in the PDF file will not be sent to his company. The file will be made to look like an official company’s PDF but all the data you input will be sent to the hacker. The automatic background running applications scan the user’s drives and upload them to a place where the hacker can view and use them for personal gain.
- Using the Data Manipulation vulnerability, the Shadow attack can change the view of the document. For example, the hacker made a PDF file where the victim will enter his bank details and transfer some amount of money to his account. After doing this the hacker creates a viewable layer that asks the user to input bank details for a 1$ donation. The viewable layer will act as a mask for the harmful content preventing the user or the signers to see the hidden threat.
- The Code Execution attack allows the attacker to run arbitrary applications using a file path, URL, or even a file embedded in the PDF itself.
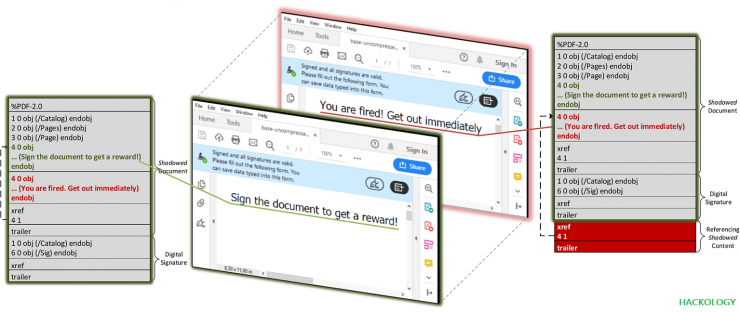
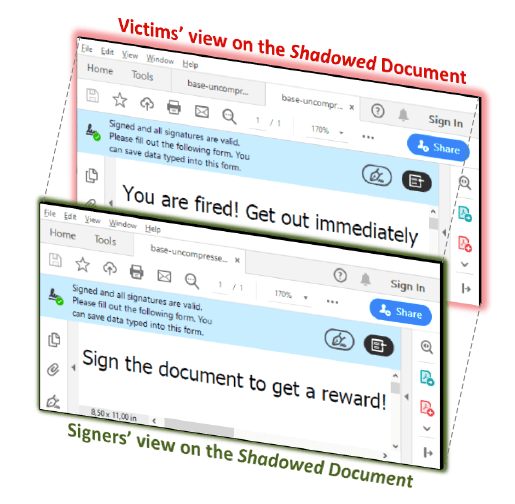
Attackers prepare a shadow document. In the analogue world, this is the step in which the attackers could explicitly leave empty spaces. The Signers of the PDF receive the document, review it, and sign it. The attackers use the signed document, modify it, and send it to the victims. In the analogue world, the attackers can print their content on the prepared empty spaces. After opening the signed PDF, the victims’ PDF viewer successfully verifies the digital signature. However, the victims see different content than the Signers. We introduce three variants of the shadow attacks, which allow attackers to hide, replace, and hide-and-replace content of digitally signed PDFs.
Ruhr University Bochum researchers.
Shadow Attack Variants
There are three variants of the attacks PDF Shadow Attacks:
- Hide
- Replace
- Hide-and-Replace
Hide is masking the contents behind a visible layer. For example, a user is sent a 1000$ money transfer, but this content is hidden behind a 1$ donation to charity content.
Replace is making changes to the file. The signatures are automatically removed if a person makes harmful changes but changing fonts is considered harmless. If the PDF is signed the attacker changes the fonts and descriptions of the forms. The original form signed was titled a 1$ charity, it gets signed. The attacker changes the font and description to a 1000$ money transfer and adds the 1$ charity reference (hint). Hints and titles have no difference in PDF documents. The PDF considers this as a harmless change and will not remove the signatures and will not alert the user that any changes were made.
Hide-and-Replace is the biggest threat as it combines the features of both variants. It contains a second hidden document with malicious content that can not be detected by the signers. After the document is signed, the attacker can amend the reference.
The Hide-and-Replace attack variant is the most powerful feature, since the content of the entire document can be exchanged,
Ruhr University Bochum researchers.
Conclusion
The first Shadow Attack broke into the PDF Signatures and manually made changes to them. The most recent second Shadow Attack found workarounds to keep the PDF Signatures after changing the layers and contents of the PDF. Here is the full PDF report published by the team “Attacks bypassing the signature validation in PDF – Vulnerability Report.” The patches were made available and the vulnerability reports were disclosed later. You can track the Shadow Attacks by these CVE-2020-9592 and CVE-2020-9596 identifiers. You can stay safe by knowing how common hacks work and ways to prevent them from happening.










Add comment