Yes, only one image can indeed crash your smartphone. An image is being shared on the internet that has killed/crashed many Android Devices. The image has adverse effects on different models of Samsung, Google Pixel, OnePlus, Nokia and Xiaomi. So far, it soft bricks many phones putting them into a boot loop and the only solution to get away is to factory reset. However, if you have unlocked your bootloader there is a way to get back your phone without doing a complete factory resert. Some smartphones didn’t show the effects. Why it happens , What is the image and How to fix the issue all will be shared in this post.
This particular issue has been reported earlier in March 2018, but that time it wasn’t happening with everyone. So, it was ignored by Google and the issue was closed. At the moment, the status shown in the issue tracker is fixed while many users are commenting that it doesn’t seem fixed.
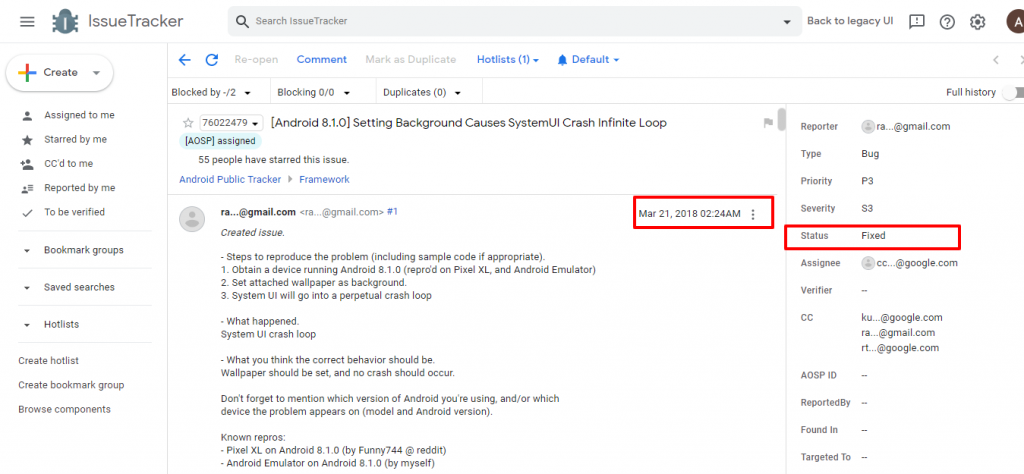
Recently, this issue has been highlighted by a twitter user Universe Ice and was confirmed by many other users. The issue may also be reproduced on android emulators such as Android Studio.
[Demo] Wallpaper Killing Android Devices
Why the Image Kills Android Devices
The issue is probably with the color profile of the image, which is exceeding the limit that android handles hence resulting in soft brick/boot loops. The image has an embedded color profile, Google/Skia/E3CADAB7BD3DE5E3436874D2A9DEE126, which may have been encoded incorrectly to crash systemui somehow since Android uses Skia in their frameworks (com.android.systemui.glwallpaper.ImageProcessHelper) . SKia is crashing from an Array Index Out Of Bounds Exception.
Although it is still not confirmed by Google nor any confirmation/patch of the issue from Google has been released.
It may affect many android smartphones and can be misused by putting this image on mobile wallpapers sites. Users may download the image and when they set it as a wallpaper, their phone may crash and result in infinite loops. So, we urge Google to create a patch quickly to avoid any misuse of such images.
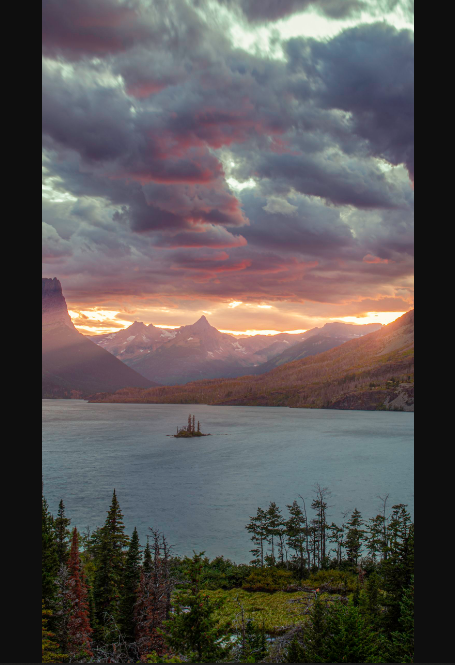
The Image That Bricks Android
The image you can see below is the screenshot of the actual image, however if you are the dare devil and want to play in dangerous territory you may download that image in its original format from HERE (G drive). Be cautious as it can put you in trouble if you set it as your wallpaper. You can try to set this Wallpaper inside Android VM VMOS and it will only quit the Virtual Machine and not ruin your actual device.
Perfect Explanation by Mrwhosetheboss
Mrwhosetheboss explains the killer wallpaper issue in a beautiful manner, after watching the video you will know everything about this issue.
How to Recover from Android Killer Image
If your bootloader is unlocked and you have a custom recovery installed, you are in luck. You can delete wallpaper and wallpaper_info.xml located at /data/system/users/0 by using file manager and your rogue wallpaper will be removed thus allowing you to turn on your phone normally.
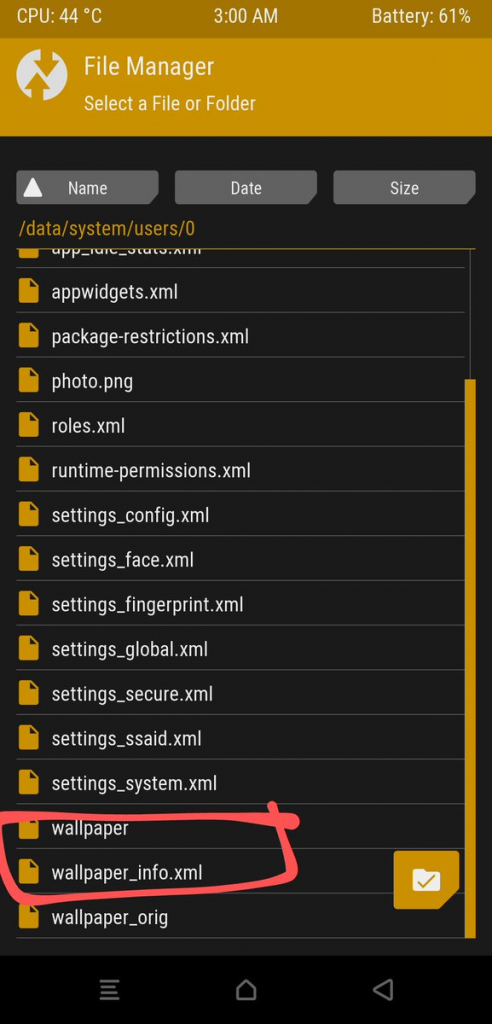
If your phone doesn’t have unlocked bootloader the only solution is to do a factory reset / hard reset of your android phone from Bootloader Menu.
Conclusion
Please don’t try this on your daily driver phones. Although if you have an extra unused android phone at home and you are ready to lose its data, you can try if it crashes your android phone and share your experience with us.
Stay connected. We will keep you updated regarding the issue.
p.s. Smartphones are effected, iPhones are not prone to this issue.










cool