Facebook has launched a new feature to assist in finding security flaws in Facebook, Messenger and Instagram Android apps for bug bounty hunters.
Since all Facebook Android products use security mechanisms such as Certificate Pinning to ensure traffic integrity and confidentiality, it is difficult for white hat hackers or security researchers to intercept, analyze network traffic and find server-side flaws.
Certificate Pinning is a safety mechanism that prevents users of an application from suffering network-based attacks by automatically rejecting the entire connection from sites with fake SSL certificates.
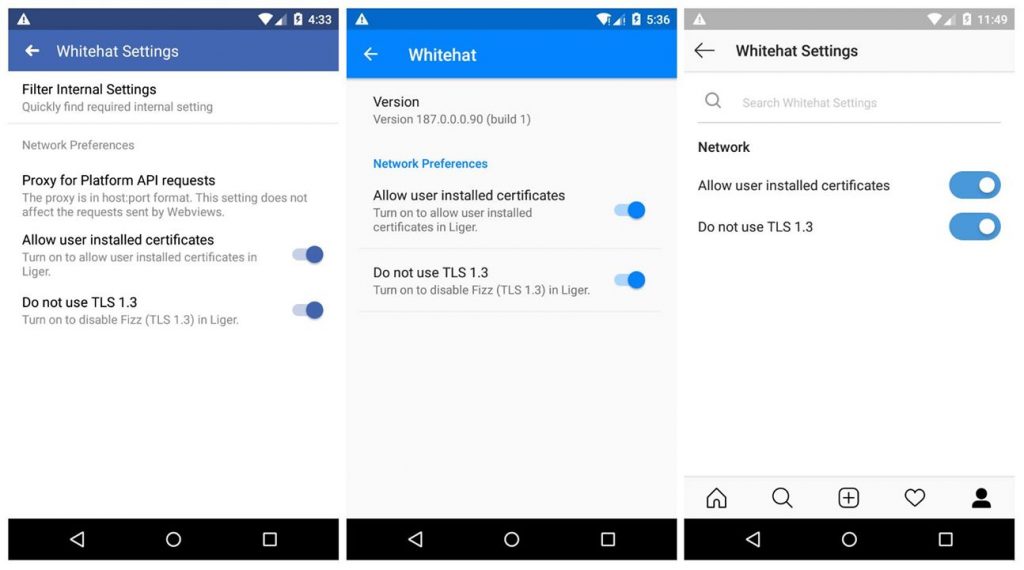
The new option, known as “Whitehat Settings” now allows penetration tester to disable Certificate Pinning on the Android apps by:
- Disabling Facebook’s TLS 1.3 support
- Enabling proxy for Platform API requests
- Using user-installed certificates
This allows researchers to pentest Facebook App including Messenger and Instagram, Facebook says,
Choose not to use TLS 1.3 to allow you to work with proxies such as Burp or Charles which currently only support up to TLS 1.2.
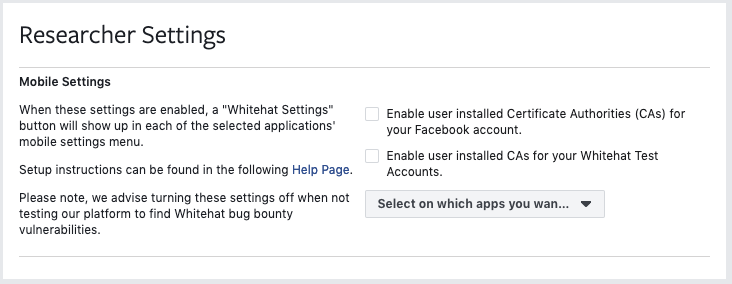
The settings are not visible by default to all. Researchers should instead explicitly permit this function from a web interface on the Facebook website as shown in the steps below, where you can allow Facebook,Messenger and Instagram android apps.
Facebook also says,
To ensure the settings show up in each mobile apps, we recommend you sign out from each mobile app, close the app, then open the app and sign in again. The sign in process will fetch the new configuration and setting updates you have just made. You only need to do this once, or whenever you make changes to these settings.
When activated, you’ll see a message at the top of your app, which says “network testing enabled – Traffic may be monitored“.
“Whitehat Settings” can be used to test Instagram app for security vulnerabilities, but for Instagram White Hat settings to appear on the Facebook website you have to link your Instagram app with your Facebook account.
It is important to be aware that Whitehat Settings are not designed for everyone to use because it reduces the security on your device for Facebook apps.
How to Enable Facebook Whitehat Settings
As mentioned earlier in the article, to access these settings in family of Facebook owned apps , you must first enable the settings through web UI. Follow the guidelines below to enable these settings from the web interface,
- Visit Facebook Bug Bounty Info Page
- Click Researcher Settings, On the left menu
- Check all that is required:
- Enable user installed CAs for this account
- Enable user installed CAs for your test accounts
- Select apps (Facebook, Messenger, and/or Instagram) to apply these settings on . You can select more then one app in the drop down menu
- Force Stop and Restart the android app
- Enable Whitehat Option on your Android App as explained on Facebook Help :
- Facebook : Menu > Settings and Privacy > Whitehat Settings > Enable what’s required
- Messenger : Click on your profile picture > Click on Whitehat > Enable what’s required
- Instagram : Click your profile picture > Bookmark Icon > Settings > Internal > Whitehat Settings. Enable what’s required
You will have option to allow user installed certificates and revert back to TLS 1.2 while Facebook App would present you with an additional option of allowing Proxy for Platform API requests. Once you perform the steps in Web UI you will start seeing the options of whitehat settings in the corresponding android app aswell, if for some reason you may not see the options you may log off and sign in to refresh the cache.
It is a very good step taken by Facebook where they have catered the requests of various researchers and it will allow them to perform some intense bug bounties. Let us know what you think about this step taken by Facebook in the comments below.










[…] White Hat Hackers : These are the type of hackers with good intentions. Often referred as ethical hackers. They might be working for the government, companies or even freelancing but their aim is to make the internet a more secure place to be. We can also call them Anti-Black hackers (see below). Their main aim is to stop black hat hackers. For example: Tsutomu Shimomura a white hat (ethical) hacker Shimomura is renowned for assisting FBI to stop Kevin Mitnick (a black hat hacker who later turned into a white hat ) who performed a number of cyber crimes and later he personally launched attacks against Shimomura’s terminal network. White hat hackers also take motivation when they get paid, that is way all the big companies now hire hackers who are paid when they find a bug, Facebook is also part of it since they launched White Hat Program for Hackers. […]