Let’s start with the main question, What Is Hacking? Hacking is basically doing something which you are not supposed to do. Sounds easy? Hacking is bypassing security measures set in place and gaining access to information and authorization which can be used to manipulate the object as per the hacker’s desires. Cyber Threats are not going to stop as technology advances, threat’s advance with them. Cyber Threat Intelligence Report 2019 shows the same analytics that even our smartphones are at risk now. A person can opt for many ways to hack something which may include:
- Keylogging
- Phishing
- RAT / Trojan Horse
- Malware / Viruses
- Spoofing
- SQL injection
- and the list goes on and on ….
‘Hackology’ might seem dangerous as a word but it merely means ‘The Study of Hacking’
Just because a word has a ‘hack’ in it, shouldn’t make you worried about it as not all ‘hack’ related words are bad or mean something negative. Hacking is a good sport too, its just how it is being implemented
The key thing is to specialize in a few and to have basic knowledge of the others because
A Jack of all trades,master of none, but oftentimes better than master of one

Another argument which raises here is that one should learn just one skill and get mastered on that, which might see useful in any other industry. So why go through each and every type of hacking skill set? A few reasons are listed below: But before that if you are very much interested in learning the skill you may consider learning it through some CEH Training provided.
- Hackers can use their knowledge to make a website or any software less prone to other hackers but this requires know-how of every hack because excelling in prevention of one type while disregarding other vulnerabilities may lead to disastrous situations.
- People hire different experts, those who have keen observation on network deployment and security architure and while they hangout with the same lot they know what are the latest trends and 0days in the market. Hired hackers are asked to make software / system secure by finding loopholes a.k.a ‘by hacking them’. Companies hire Hackology services so they can do a full throttled Penetration Testing and provide a post pentest report so companies can secure their systems if that is required. If you just focus on one hacking skill you won’t be able to provide multi prong attack vectors.
- Diversity is a key which helps people. Basic knowledge of all the hacks will prove useful in making your product more secure.
Hacking doesn’t necessarily mean that you type a few words and in under a minute you can activate a time bomb and decimate the whole city/country. No, it means hours and even days or months of rigorous work to achieve a single objective in our case “to hack something.” Which requires extensive knowledge of hacking methods.
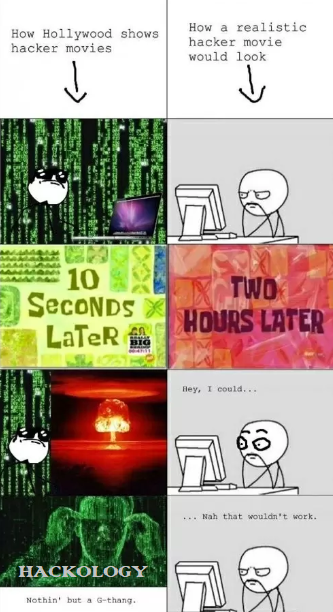
A normal person is fascinated when they see a hacker in a movie because that particular “pushing the keys forcefully with sweaty hands and forehead in an intense life and death situation, hacking the thing near the last second and having a sigh of relief” scene. That doesn’t happen here. It takes time to succeed, mostly people stop learning or working just because they do not find this viable after a few days. While learning or working try to focus and hold your ground. Nobody cares about you until you accomplish something. They see a man standing on a stage and everyone cheers for them what they don’t know or care about is how many sleepless nights and work has helped that person to stand on that stage. Social Engineering is not easy to pull off but people only see the end result of a success story.
Types of Hackers
We can classify hackers into numerous groups but the main types of hackers are
- White Hat Hackers : These are the type of hackers with good intentions. Often referred as ethical hackers. They might be working for the government, companies or even freelancing but their aim is to make the internet a more secure place to be. We can also call them Anti-Black hackers (see below). Their main aim is to stop black hat hackers. For example: Tsutomu Shimomura a white hat (ethical) hacker Shimomura is renowned for assisting FBI to stop Kevin Mitnick (a black hat hacker who later turned into a white hat ) who performed a number of cyber crimes and later he personally launched attacks against Shimomura’s terminal network. White hat hackers also take motivation when they get paid, that is way all the big companies now hire hackers who are paid when they find a bug, Facebook is also part of it since they launched White Hat Program for Hackers.
- Black Hat Hackers : These are criminals who hack for their personal gain, it might be for fame, fun, information, money, data or anything they can find to hack. They go against the law for personal gain.
 For example: Albert Gonzalez from 2005 to 2007, his cyber group including him had allegedly sold approximately more than 170 million credit cards and ATM numbers. One of the biggest cyber theft in history. You may be interested in reading about the World’s top 10 Black Hat Hackers ? Black hat hackers have done nasty things, like taking down internet cables of a country, Using your computer to Mine for Hackers, Releasing largest Android based Malware Attack or showing us the most advanced phishing attack vector. But not all the bad persona on the internet you see is of actual black hat hackers , some are even scammers trying to scare you into submission and some are even impostors on the darkweb.
For example: Albert Gonzalez from 2005 to 2007, his cyber group including him had allegedly sold approximately more than 170 million credit cards and ATM numbers. One of the biggest cyber theft in history. You may be interested in reading about the World’s top 10 Black Hat Hackers ? Black hat hackers have done nasty things, like taking down internet cables of a country, Using your computer to Mine for Hackers, Releasing largest Android based Malware Attack or showing us the most advanced phishing attack vector. But not all the bad persona on the internet you see is of actual black hat hackers , some are even scammers trying to scare you into submission and some are even impostors on the darkweb. - Gray Hat Hackers: This is the confused lot and this is also the majority lot. Gray hat hackers are Hackers who would leak a cyber breach data on the internet for everyone to enjoy with no gain of their own. They might find a bug, loophole or anything which can be used against someone and they will post it online or they might inform the proper authority.In short they are the buggers – they will behave good if they want to and play evil if they desire but in both the cases, personal gains, fame or money might not be the motivation. Their methods may sometimes be wrong and not legal but they don’t do it for their gain unlike black hat hackers. For example: Khalil Shreateh, was an unemployed computer security researcher and in August 2013 he exploited Facebook and managed to post on wall of Mark Zuckerberg, normally no one can post on walls of other Facebook users especially if they are not your friends and have set ‘Friends only’ privacy. He did this after the security team refused to consider it as a bug. His act of posting on the wall of CEO of Facebook was just to make his point, so that Facebook can take action and fix the bug he found. Facebook did fix the bug but he was denied any fee
- Hacktivists: These are the hackers who hack to make a social or a political point or they want change according to what they think might be right. Anonymous and SEA (Syrian Electronic Army) are such two famous Hacktivist Groups. For example: Anonymous hacktivists in February 2017 took down more than 10,000 sites which were related to child pornography.
- Script Kiddies: These are fairly new people trying to learn hacking. Also known as “Noobs” among hackers. They use existing software, pre-written scripts and anything that can be copied and use them and get called “hacker” for doing so. They lack the actual expertise and don’t do anything themselves. For Example: All the people who use cheat engine, already made keyloggers and dDoS attacks are usually script kiddies. Although a latest trend suggests, that not everyone have to invent the wheel and making use of existing tools might not be a bad thing, but those who go out and about and getting called 1337 are those who would fall in the script kiddies criteria.
Learning tips
Go and search on “Google“. That’s it. Nothing more to see here. Any query, problem and literally anything you can find their answers on Google. Hackers ‘read’ they read alot and learn from it and practice to polish their skills. There are NOT PROGRAMS which you can download and enter a user Facebook
Numerous forums are available where people like you have asked professionals for help and got enlightened responses. Sometimes experienced people get frustrated because of basic questions being asked again an again that’s why sometimes they call the learners ‘noobs’. However that should not stop you from learning. An advice from a friend of mine, Start of with SQL injection and install Kali Linux or any of your favourite Pentesting OS and explore and learn . If you have interest in this field you will start picking things up. This article is aimed at the newcomers because even what has been shared here is very basic and there are lots more to it. Once you set your foot inside the hacking domain and you find it interesting, you will start looking out to learn more and that’s where the real journey begins
That’s all folks, please comment on what to add in the article so we can help newbies. Who knows that one day they might be the only hope and standing as your defense between your Cryptocurrency and a black hat hacker.


 For example: Albert Gonzalez from 2005 to 2007, his cyber group including him had allegedly sold approximately more than 170 million credit cards and ATM numbers. One of the biggest cyber theft in history. You may be interested in reading about the
For example: Albert Gonzalez from 2005 to 2007, his cyber group including him had allegedly sold approximately more than 170 million credit cards and ATM numbers. One of the biggest cyber theft in history. You may be interested in reading about the 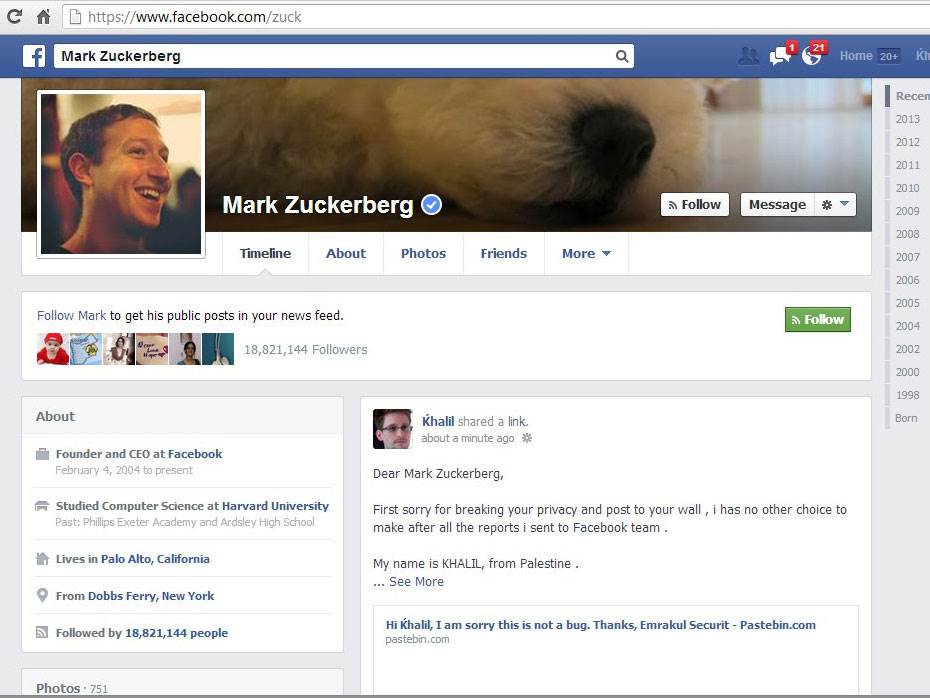







Add comment