In this world of technology and IoT we connect everything to the internet, connected peripherals mean that we share data and its on the cloud even more then you can imagine.
How to know if you are Hacked ?
Being hacked in literal sense always meant that someone targeted you and gained access to your account but now a days people get hacked with a different approach. Once online services get hacked, Hackers release or sell the user information and that is the time when your data and account is PWND even without your knowledge.
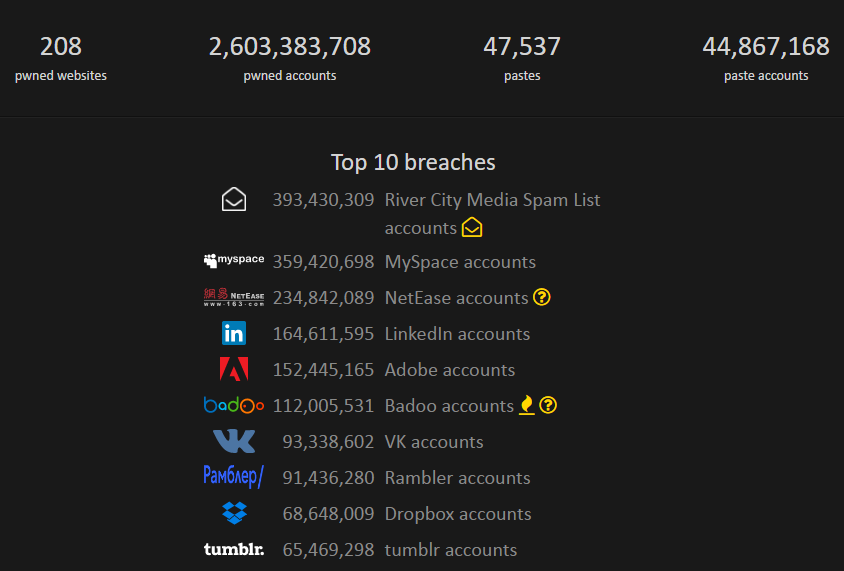
Have I been pwnd? is the service which lists 2,603,383,708+ Accounts and a dozen services, every hacked data is updated into the database and you can simply check if your account has been hacked or not.
Check if you have been PWND
Step 1 : Open Have I been Pwnd?‘
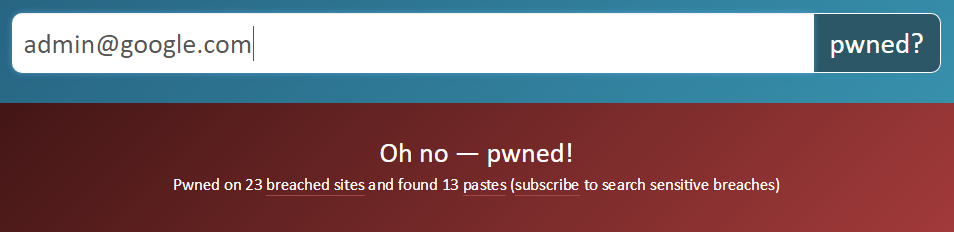
Step 2 : Enter your email address or Username and hit “pwnd?“
Step 3 : If you are a heavy internet user you will see a list of services whose data has been breached and your entered Email Address / Username is part of the breach. In this example I checked if [email protected] has been breached and guess what it has hacked data on around 23 Websites
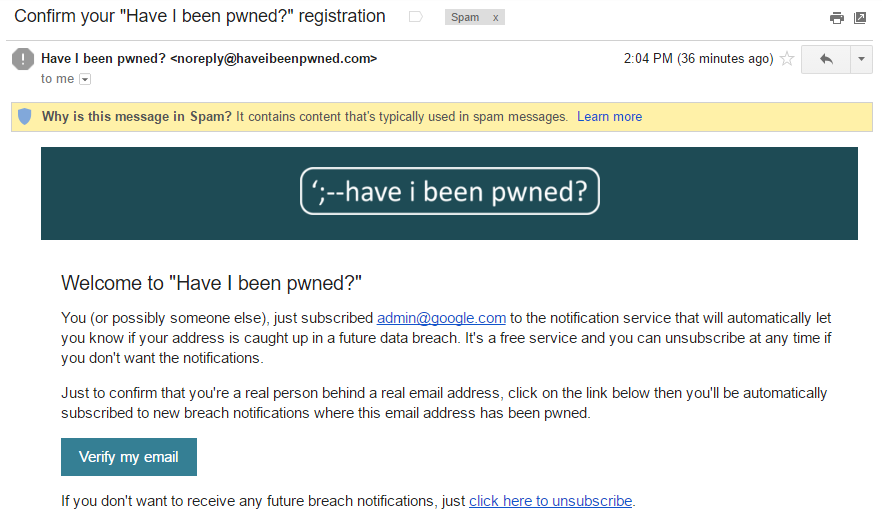
Step 4 : If you have no PWND account data, feel happy !!! But what if some service you use gets PWND in future ? use the Notify Me Service to get notified if your Email Address surfaces on the Dark Web with your password some time later. Verification Email from Have I been PWND? will land in your Junk so do check out the Junk Folder and Confirm your email
What to do if you have been PWND ?
Simply “Change your Password” , first change the password of the email you searched and later change the password of the services listed and Follow these Password Techniques, Also note stop using your old password as it has already been added to the password list used by Hackers










[…] have already shared about a service which allows you to see if your Email Address surfaced in any Hacks on the internet, a good way to […]
[…] important but it’s also important not to use that same password on other services and once it gets exposed it is no more […]
[…] In today’s era everyone and everything is connected with Internet and all our data is being shared in ways we can not understand. It is common for us to read about various services and people personal data being hacked. Because the amount of being shared has increased as data speed and their fares have reduced. I can place a bet that if you check all your email addresses you ever used, there is a 99% chance that atleast one of your email address / password would be exposed / hacked, Don’t believe me ? View Your Hacked Accounts. […]
[…] Whatever you do, DO NOT PAY. If you have received such an email you can Contact Me Discreetly or Ask Techie for a customized answer. You may follow This Guide and also see View your Online Hacked Accounts. […]