Few months back it was Ufone injecting code into users web traffic by replacing Google Analytic Code. This time its Zong, a Cellular Company in Pakistan Owned by China Mobile performing even more unethical activity by injecting Malware code into mobile Data users of Zong, showing a total lack of interest by Zong to protect its Users.Such code injections mean that they are tracking and can modify all our online activity for their Advertisement and Financial gains. A Technical explanation of the injection is below
Zong Internet Traffic Manipulation (3G / 4G)
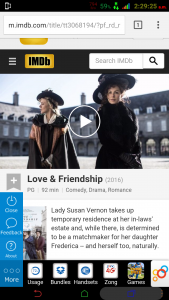
Every Zong user on mobile data is presented with a sidebar injected in every website(HTTP). Which shows a small Zong icon , once clicked it expands and gives out more options. Icon Sidebar is visible at bottom right on the image above.
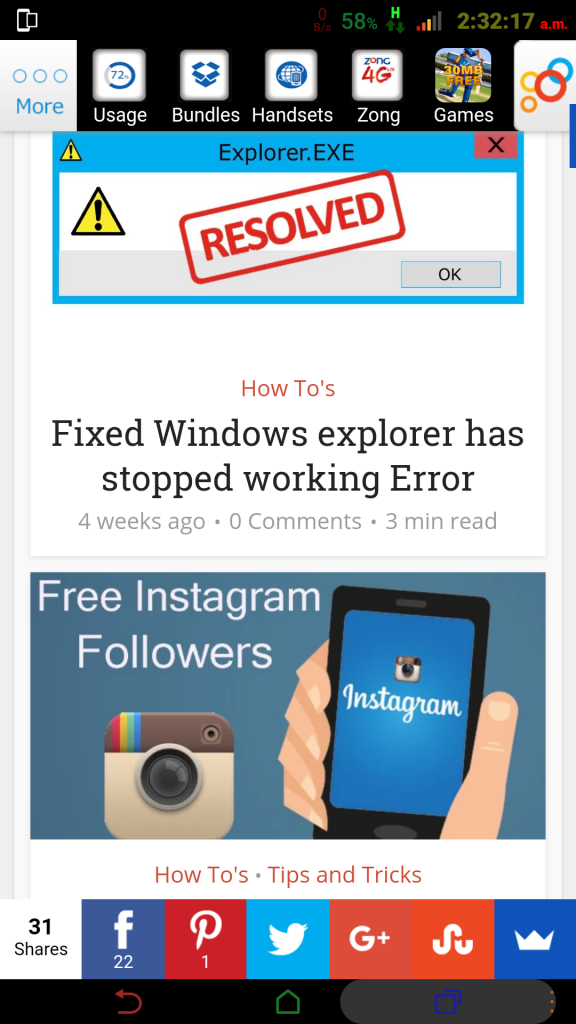
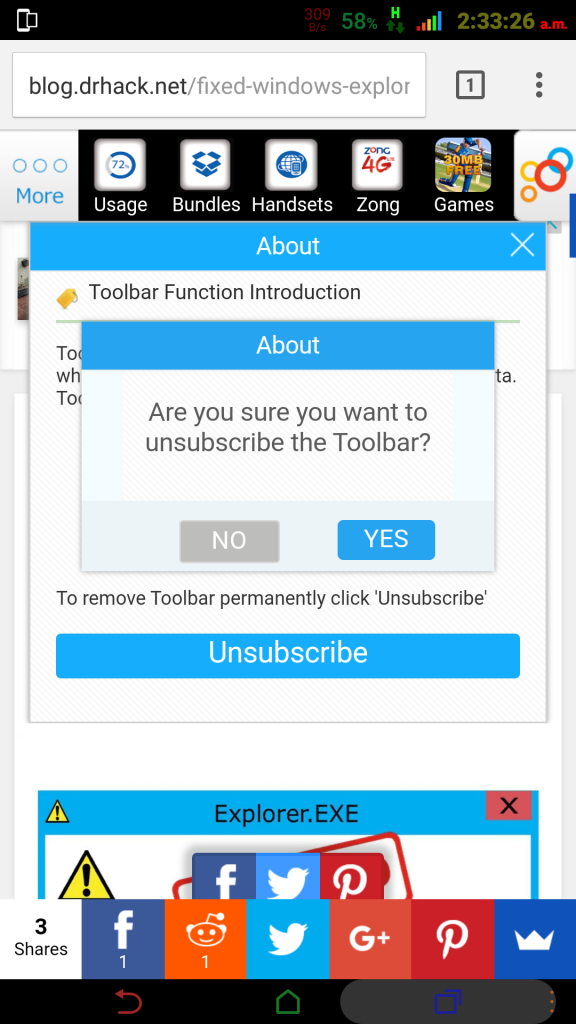
Tapping on the icon the Toolbar expands(as shown at the top of the screen on above image) and give out more options ,apart from one option rest all is advertisement which Zong is doing just because users are using their network. (Shame)
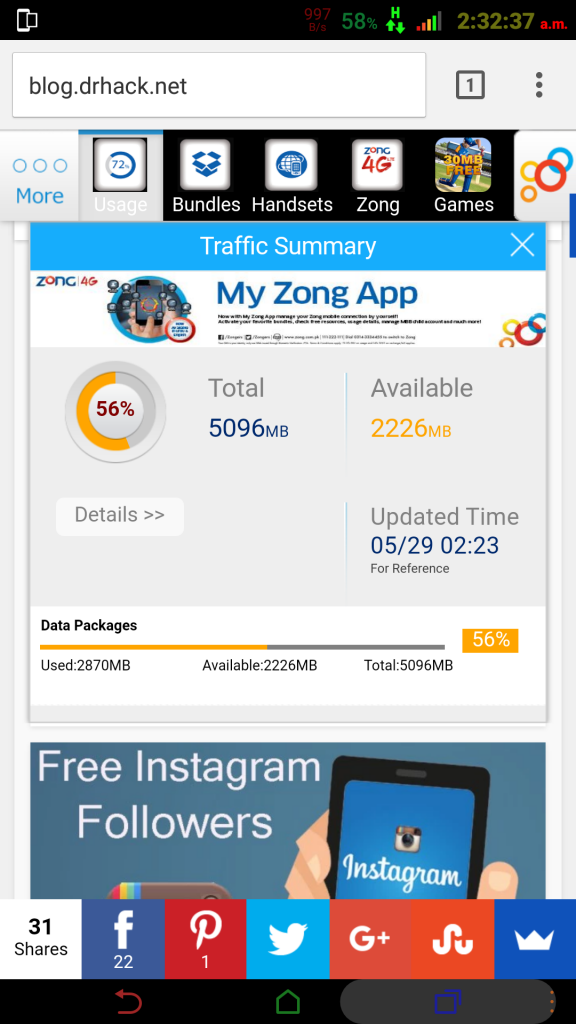
The only useful thing is the “Usage” which shows users about their data usage , else its all spam and a hindrance in user browsing experience
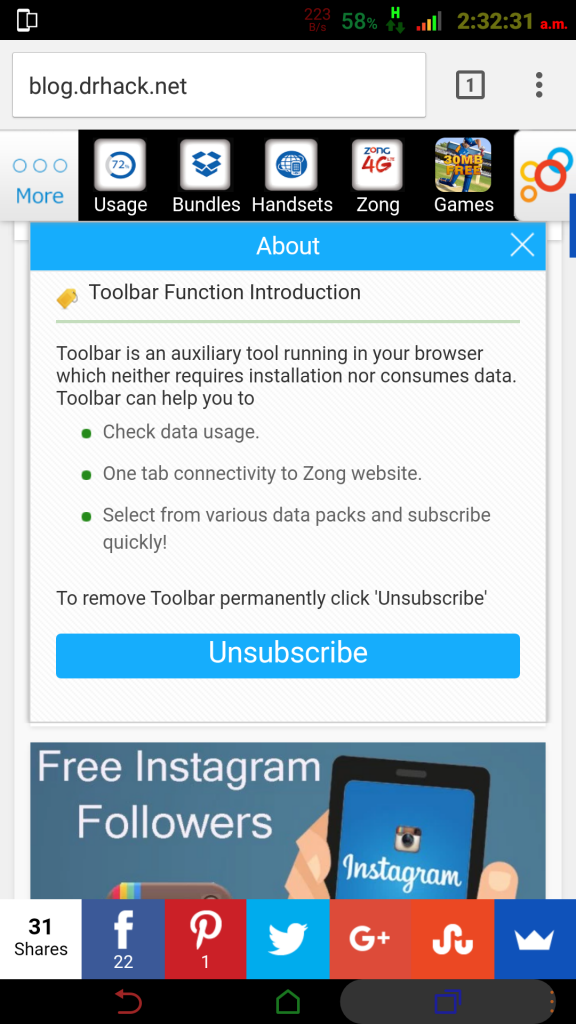
Zong is calling this unethical act of theirs “Toolbar Function”
How to Unsubscribe from Zong Toolbar (Mobile Data Users)
Although you can not completely disable code injection by using this method but you can unsubscribe from the toolbar by Clicking on “About” and hitting the “Unsubscribe” link .The toolbar will not appear anymore
The same toolbar also injects and appears for Desktop users and on every other website.
How to Permanently block the Code Injection
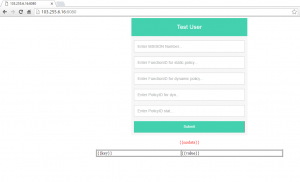
During research i came to know that the toolbar and malware is served from 103.255.6.16 IP Address. This IP is based in Pakistan and blocking it in your Firewall will get you rid of such shady practices of Zong.
Interesting Stuff on Zong Toolbar Server
Overlook of the the server gave me various URLs which reveal partial information about how Zong is injecting code in Internet traffic, please note Zong can change this anytime , they can even redirect you to any other website of their choosing.
- http://103.255.6.16:8080/ – It presents interesting forum
 103.255.6.16:8080/html/www/resources/templates/static/cmpklbar_en/pagestemplates.js
103.255.6.16:8080/html/www/resources/templates/static/cmpklbar_en/pagestemplates.js
- cmpklbar stands for China Mobile Pakistan Lower Bar
- 103.255.6.16:8080/html/www/resources/templates/common/libs/framework.js
- 103.255.6.16:8080/www/default/base.js
- If you see above JS you will see two Chinese domains (www.caijing.com.cn & www.people.com.cn )
Are SSL (HTTPS) sites completely Safe ?
No , if you are website is using Mixed SSL or Flexible SSL it means code can be injected in that site aswell. Zong can anytime make a plan to inject Google Analytics code as it was done by UFone. The only solution for webmasters is to use Forced SSL, so that all non http content is stripped OFF and not served.
Researchers ?
Researchers may explore more and share what interesting things you found out , and even complain to your local Telecom Authority so they may know this act of Zong










Well, That’s really shameful I think. PTA must take action against such practices. Manipulating the trafficking for Financial gains? Being their user, I’m going to file a complaint against them.
WTF!
If enough users like you file a complaint , cellular companies might eventually STOP doing such things .. you may share the link so that others may file report (i may add it in the post)
Even this Shady code is that much bad, it can impact your local website developement, because developer us open tag apparoch in css, such as body, div and p, it was really pain for me in first time when i was developing website for customer and i was pushing CSS but it was not working, found the shahdy code later on and disable it.
ufone also inject code i captured this
data:text/html;base64,PEhUTUw+DQo8bWV0YSBodHRwLWVxdWl2PSJyZWZyZXNoIiBjb250ZW50PSIwO3VybD1odHRwOi8vZ28uYWQydXAuY29tL2FmdS5waHA/aWQ9MjQ1NzcyIj4NCjwvaHRtbD4NCg0K
and complain to ufone as well they completely deny it
When you encountered this?
What is the procedure to file complain?
I blocked their ip and port in eset firewall and setup to alert me on every block, and it is damn blocking ip on almost every website 😀
PTA would be viable option , using their online Form : http://www.pta.gov.pk/index.php?option=com_content&view=article&id=1590&Itemid=770
well they will inject on every non ssl website .. #jerks
i dont remember as i dont use it now, i checked the file creation date it was 25th july 2015. they dont put it on every page but randomly so they dont get noticed, i found it when i saw it on my own website.
If I select ISP in this complaint form, it does not have Zong in available providers list 😛
Screenshot would help you to lodge one , even others can do so…
I am sure a decent number that goes to them , might think about it .
you can use the short code for this post link : http://bit.ly/ZongCode
the tricky thing is how they serve this randomly .. so certain folks are saying even now that there is something installed on my cell / pc thats why ads are appearing . lol
[…] last post about how Zong is injecting its own code on every website of mobile users generated a debate among the circles, including Zong on […]
[…] Zong toolbar which was being fed to its users forcefully irritated a lot of users. Zong Response was not positive initially and the twitter support came up with real alarming response. But after a days time someone from with in the company realized and amends were made. […]
[…] and capture your logs and sensitive data ? One of our admin recently had a bad experience with Zong Tool Bar Code Injection & they resolved it somehow after a lengthy discussion with Zong Management (Huh Okay ? ), […]